How an AI Tool Triggered the Vercel Security Breach
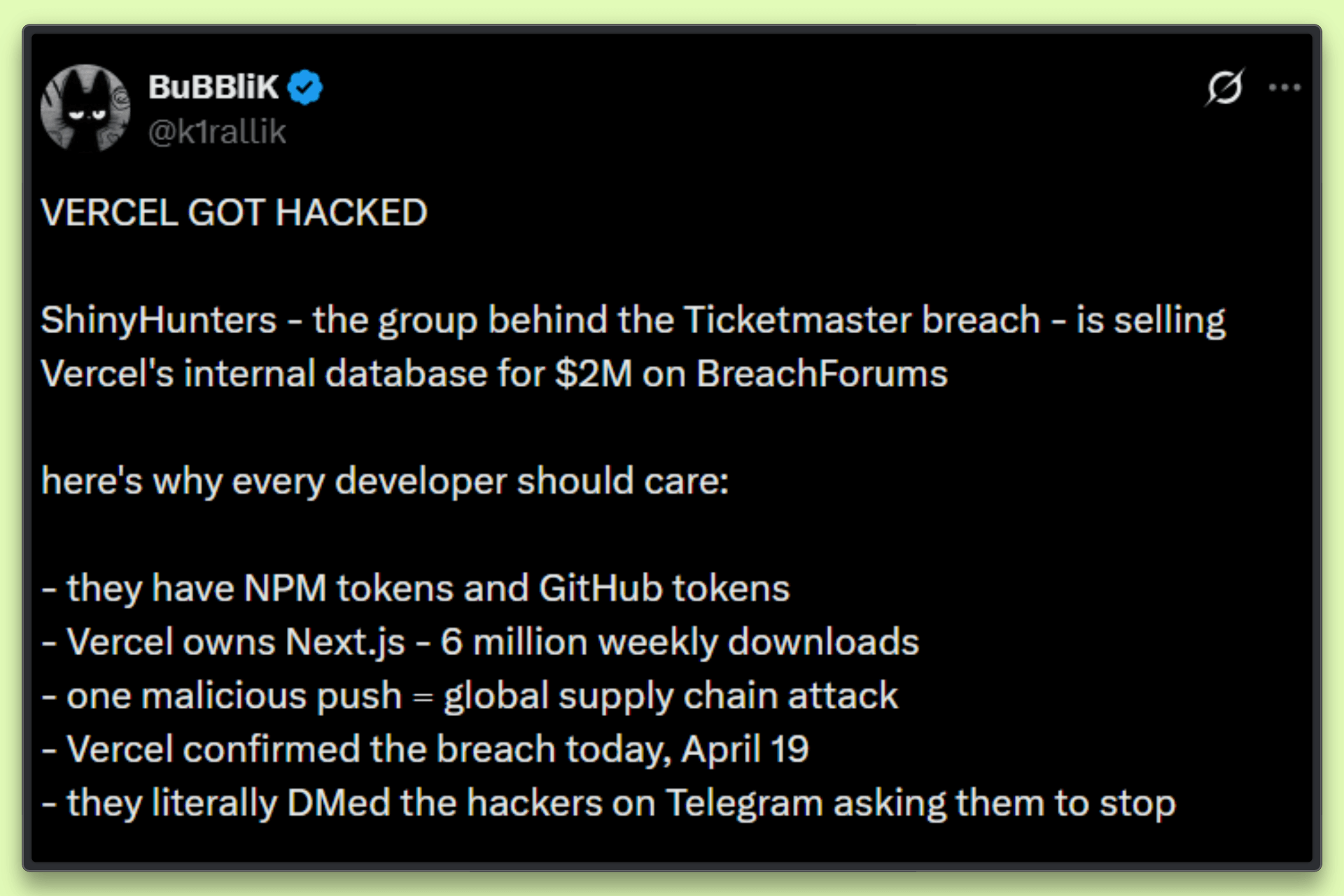
On April 19, 2026, Vercel, the cloud deployment platform behind Next.js and a key hosting layer for many web applications, confirmed a serious security breach. Unauthorized actors gained access to internal systems, prompting law enforcement agencies and incident response teams to become involved and prompting urgent credential rotation efforts across the developer community.
Early findings show that the incident did not come from a zero-day flaw in Vercel’s core infrastructure. It began as a supply chain attack that started with a third-party AI tool on an employee’s device.
This article discusses the origin of the breach, traces how the attack progressed, and explains its impact on modern software security practices.
How It Started: Context.ai Gets Compromised
The entry point was not Vercel. The attack began with a compromise linked to Context.ai, an AI platform used by a Vercel employee.
Research from Hudson Rock shows that a Context.ai employee was infected with Lumma Stealer as early as February 2026. It extracts sensitive data from infected systems, including Google Workspace credentials, Supabase keys, and Datadog logins. It also exposed access to the support@context.ai account, which likely gave the attacker a path to move further.
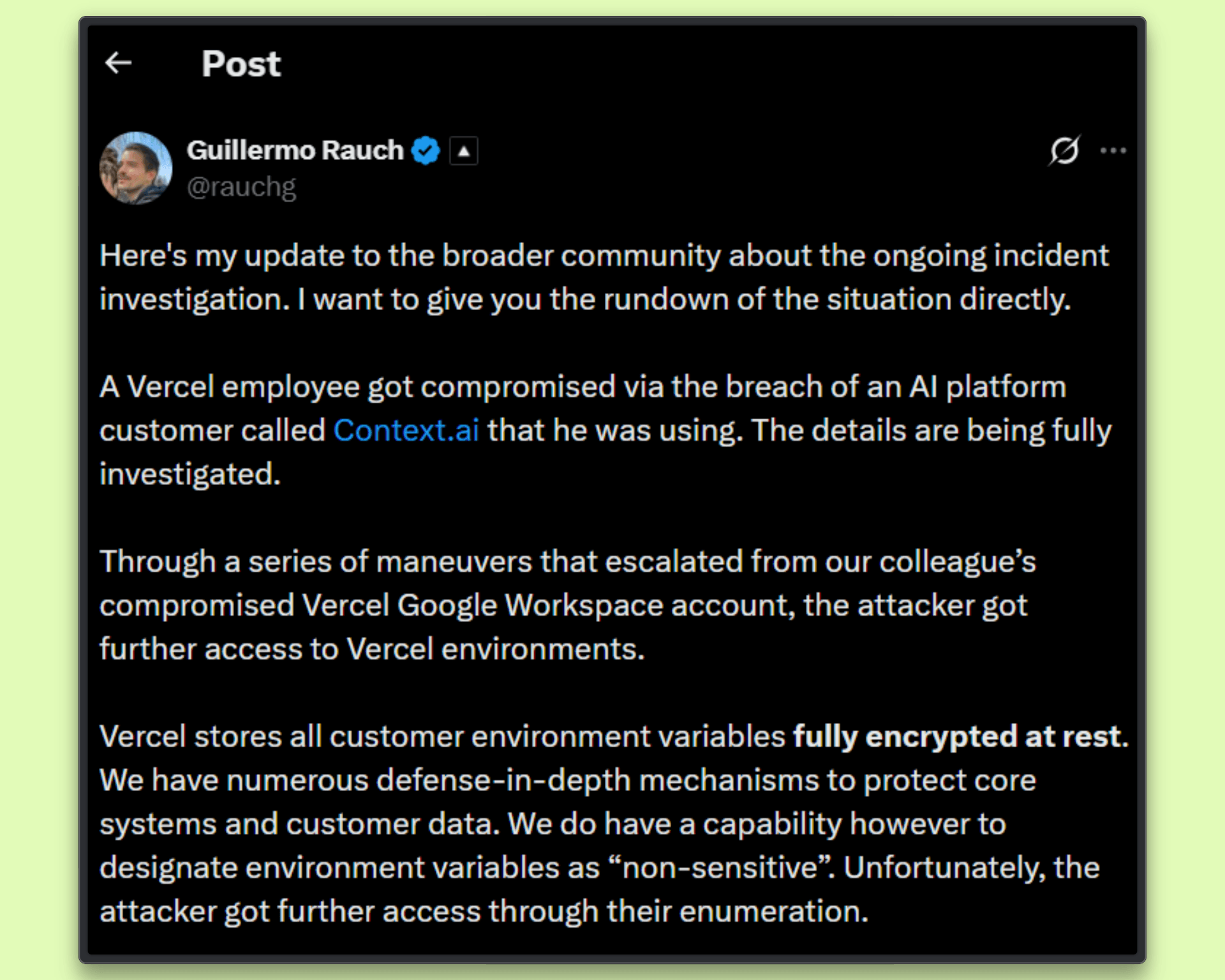
According to Guillermo Rauch, CEO of Vercel, the attacker gained initial access through this external tool. The compromise affected the employee’s Google Workspace account and became the starting point for deeper access.
How the Attack Expanded
Once inside the compromised Google Workspace account, the attacker used it to reach Vercel's internal systems.
They took advantage of Context.ai’s OAuth integration, which had broad access across connected services. These tokens remain valid for extended periods, allowing access to persist and activity to continue without immediate detection.
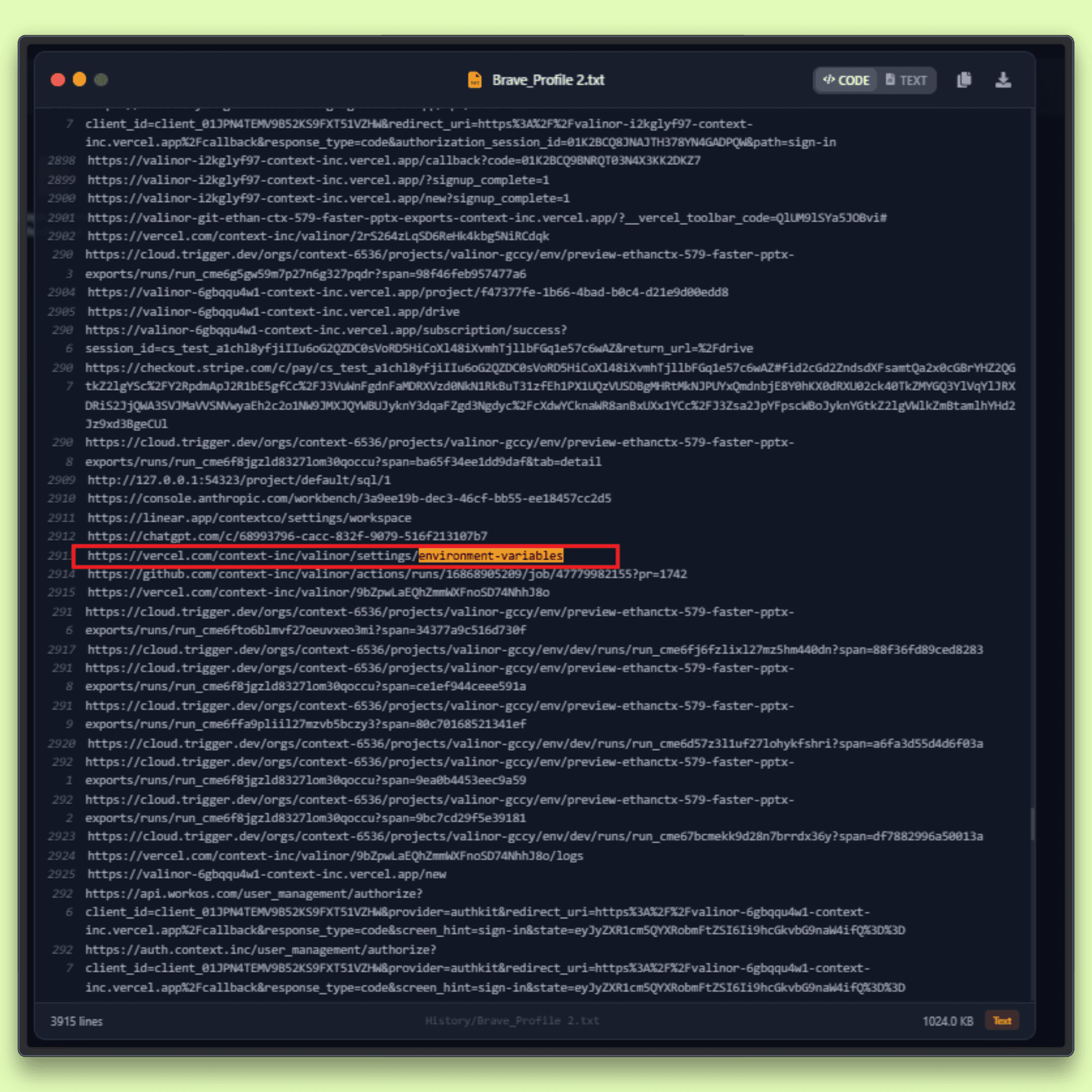
Vercel confirmed that environment variables marked as sensitive remained protected. Variables not marked this way were exposed during enumeration. These can include API keys, database credentials, auth tokens, and build secrets.
Reports from the developer community suggest the attacker may also have accessed GitHub integrations, npm tokens, and Linear workspace data. These details are not fully confirmed but align with the level of access observed.
Guillermo Rauch noted that the attacker operated with high speed and precision, with activity that may have been accelerated by AI.
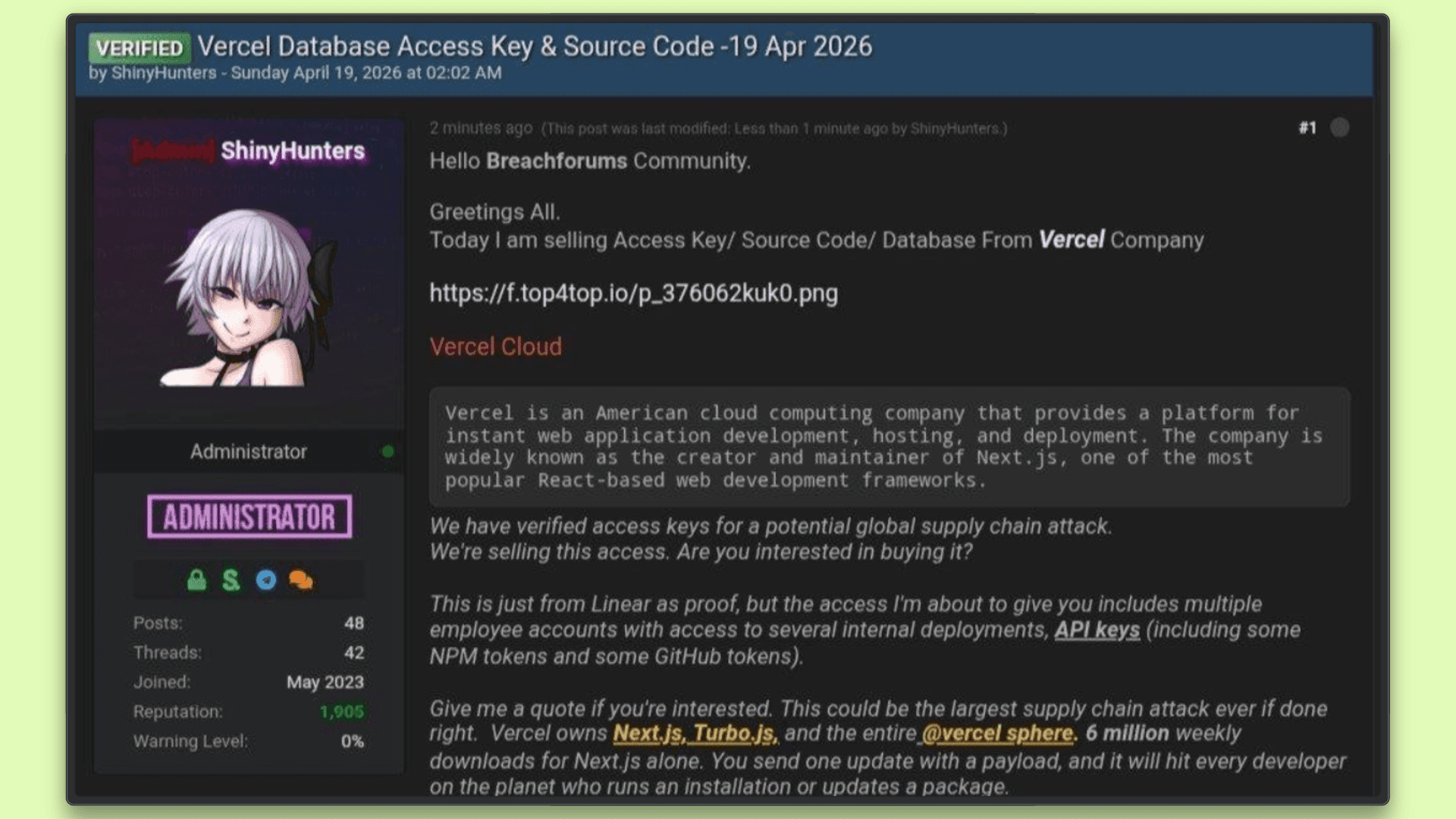
BreachForums Listing and ShinyHunters
Shortly after Vercel disclosed the incident, a threat actor claiming ties to ShinyHunters posted samples of stolen data on BreachForums.
ShinyHunters has been linked to several high-profile breaches, including the leak of data related to Rockstar Games, which adds weight to the claim, though it remains unverified in this case.
The listing reportedly included approximately 580 employee records, including names, email addresses, account statuses, and activity timestamps. This type of data can support targeted attacks such as phishing or account enumeration.
The attacker also demanded $2 million in exchange for deleting the data and preventing further leaks. Attribution remains uncertain. Threat actors associated with recent ShinyHunters activity have denied involvement, and no direct link has been confirmed.
What Was and Wasn't Compromised
To clarify what Vercel has confirmed:
Confirmed exposed: Environment variables not marked as "sensitive," access to certain internal systems, and a limited set of customer credentials. Affected customers have been contacted directly.
Confirmed safe: Environment variables marked as "sensitive" are stored in encrypted form and were not accessed. Next.js, Turbopack, and other open-source projects remain unaffected. No evidence suggests any tampering with the software supply chain.
The full scope of data accessed beyond the known employee records is still under investigation.
The Immediate Response Guide
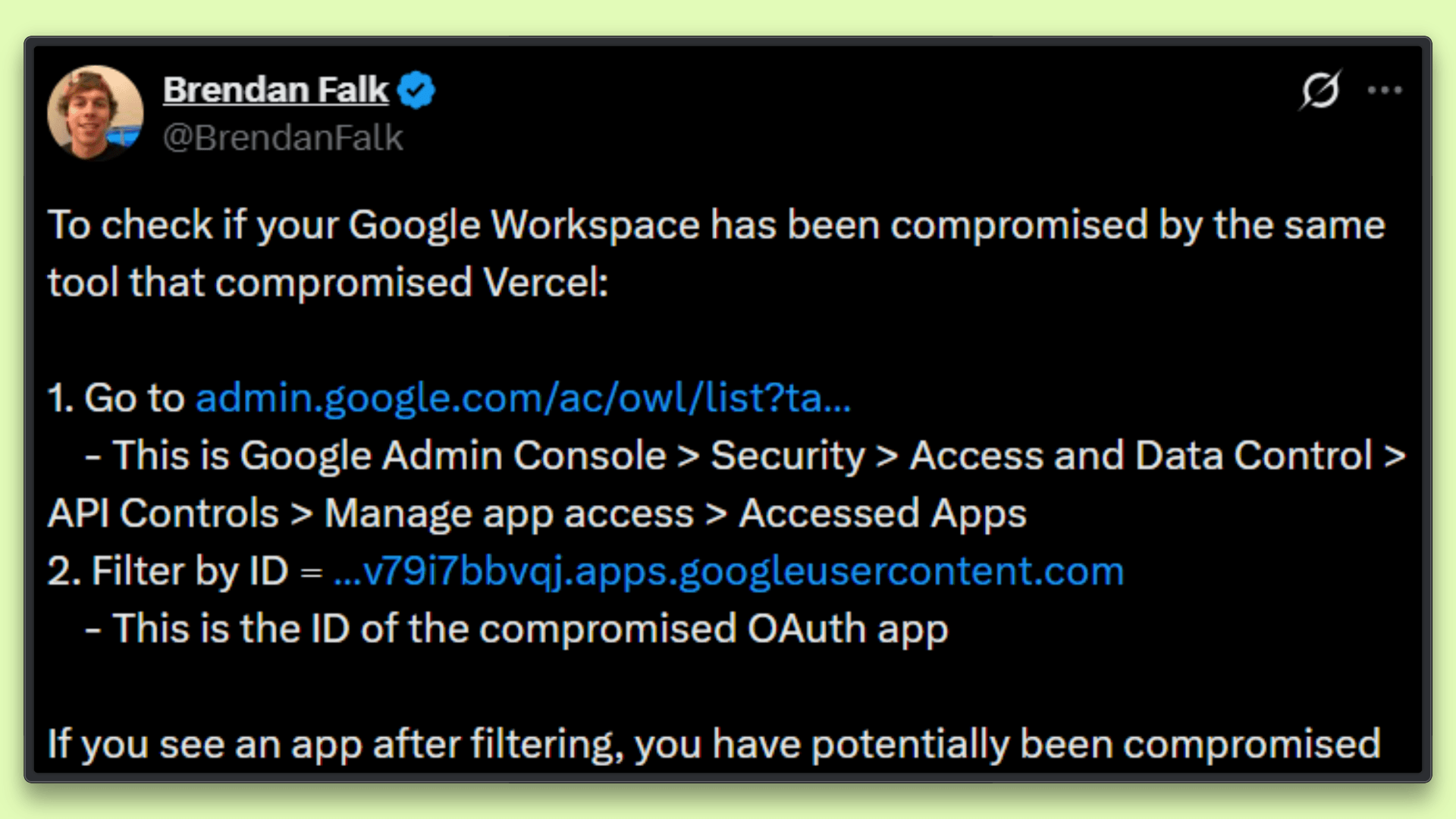
As the situation unfolded, Brendan Falk shared a practical and actionable response guide. If you are using Vercel, these steps are worth following:
Audit environment variables: Run
vercel env ls --environment productionacross all projects. Identify variables not marked as sensitive and treat them as exposed.Review Google Workspace OAuth apps: Check Security → API Controls in your admin console. Look for the Context.ai OAuth app ID and revoke it if found.
Rotate GitHub and npm tokens: Treat all tokens connected to Vercel as compromised. Revoke and regenerate them.
Inspect Linear audit logs: If your team uses Linear, review Workspace Settings → Security → Audit Log. Look for exposed secrets such as
AKIA,sk_live_,ghp_,ghs_, ornpm_, and rotate them.Check recent deployments: Review deployment logs for unusual activity. If anything looks suspicious, remove the deployment and redeploy from a clean state.
Use April 1, 2026, as a safe starting point when reviewing logs for potential exposure.
The Bigger Picture
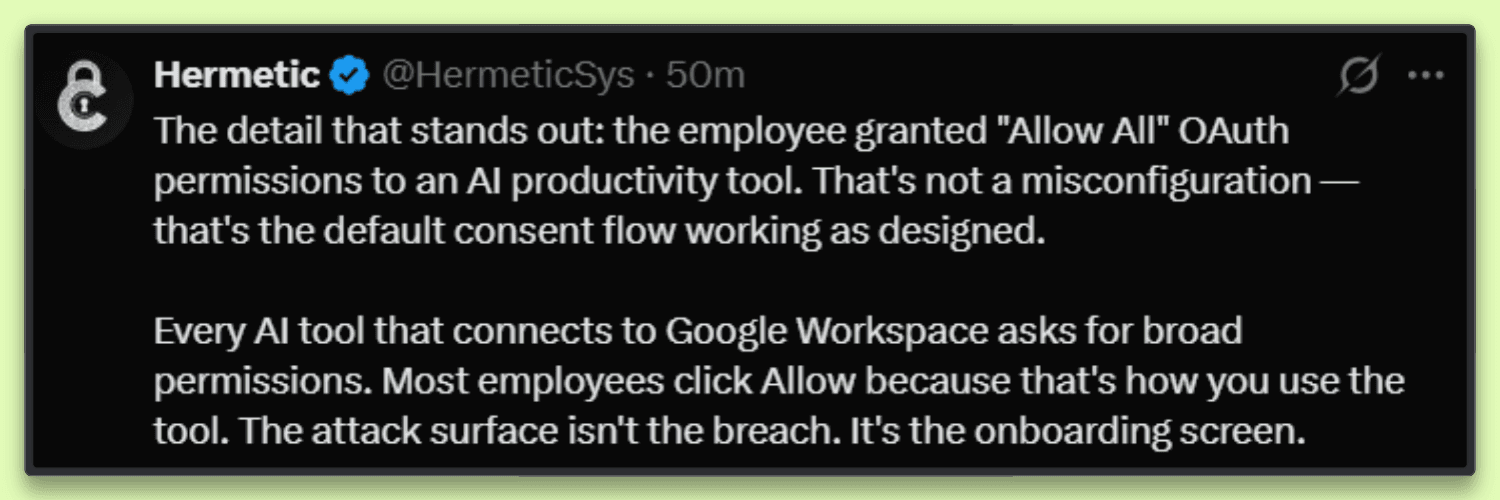
This incident points to bigger risks in how modern systems connect and operate.
Trusted tools and integrations can serve as entry points to core systems. Access through a single connected service can extend across multiple internal environments.
A design gap in environment variables played a role. Many credentials remained accessible because they were not marked as sensitive, even though they included production-level secrets.
Millions of applications rely on Next.js. Reports of access to GitHub and npm tokens raised concern about possible supply chain risk, even though no tampering has been found.
At the same time, Vercel was reportedly preparing for an IPO after strong growth. Incidents at this stage bring added scrutiny from users and investors.
The response moved quickly. Mandiant and other security teams were engaged. Law enforcement was notified. Affected customers were contacted, and new controls for the visibility and management of environment variables were introduced.
The investigation is still ongoing, and the full scope of accessed or exfiltrated data has not yet been confirmed.
The Lesson for Every Engineering Team
The Vercel breach is a clear reminder that your stack is only as secure as the weakest OAuth app connected to it. AI tools, analytics platforms, and productivity integrations now act as entry points into core systems because they are trusted, widely used, and rarely audited.
If your team uses Vercel, rotate credentials and review recent access. Any third-party AI tool connected to Google Workspace should be audited, with permissions verified and unnecessary access removed.
Tools like Enteligence are built for this environment. They provide AI-powered code review and security insights by linking findings to real incidents and team context, which helps teams identify actual risks and act faster.